This article is part of my Pi-hole series. Be sure to check out the other articles in this series for additional information.
Pi-hole Series Index
- What Is Pi-hole & Why Would You Want To Use It? — You Are Here
- Installing Pi-hole On Debian / Ubuntu Servers
- Installing Pi-hole Using Docker
- Installing Pi-hole On TrueNAS Scale
- Basic Pi-hole Configuration
- Using Gravity Sync To Sync Multiple Pi-hole Instances
- Advanced Pi-hole Config: Recursive DNS With Unbound
- Using Pi-hole Local DNS And Why It’s Important In Your Homelab
When it comes to online privacy, people generally accept that a certain amount of privacy is a smart idea. Obviously, not everyone is consistent with keeping information private – some people share more than others – but we generally feel that protecting details about ourselves to be a smart precaution.
To help protect against online predators, parents teach their children to be careful about what information they share about themselves. People typically don’t give out our home addresses or personal phone numbers to strangers online. Often, we use aliases or nicknames on social media to help protect our identity.
Privacy is good.
It is no secret at this point in 2022 (when this is being written) that Google, Facebook, Amazon and others do everything they can to track what you read, watch, and do online. Extensive profiles can be compiled based on knowing what websites you visit and how often / what types of movies and tv shows you watch / where you get your news / etc …
Some parts of the world have started putting in place legislation to help ensure the privacy of people online – for example, the EU a few years ago passed GDPR guaranteeing the rights of people who live in the EU to certain protections , access to the data others collect about them, and the ‘right to be forgotten’.
While many people are fine with this kind of data sharing, a growing number of people online are taking their online privacy a step further by actively reducing the amount of information that is gathered about us by the websites and platforms that we visit.
Pi-hole is an essential tool used by those who wish to better protect their online privacy.
What Actually Is Pi-hole?
Pi-hole is software that creates what is called a DNS sinkhole. You don’t install this software on your desktop PC, however. Instead Pi-hole was designed to be run as a separate appliance on your network. Originally, it was designed with the idea of turning an inexpensive Raspberry Pi single board computer into a low-power-use yet full-featured network privacy and security appliance. The name itself is a combination of Raspberry Pi and sinkhole.

Pi-hole doesn’t specifically require a Rapsberry Pi for us to make use of it. Any spare computer can be configured to act as our Pi-hole device. You don’t just have to have a spare physical device for Pi-hole – if you’re at all familiar with the ideas of virtual machines (example – VMware) or containerized apps (example – Docker) we can deploy Pi-hole using these technologies as well.
Regardless of where your Pi-hole software is housed, once installed and configured, it can be used by any device on your network – PCs, tablets, phones, internet-of-things devices – all of these can be used in conjunction with Pi-hole.
What Does Pi-hole Do, Exactly?
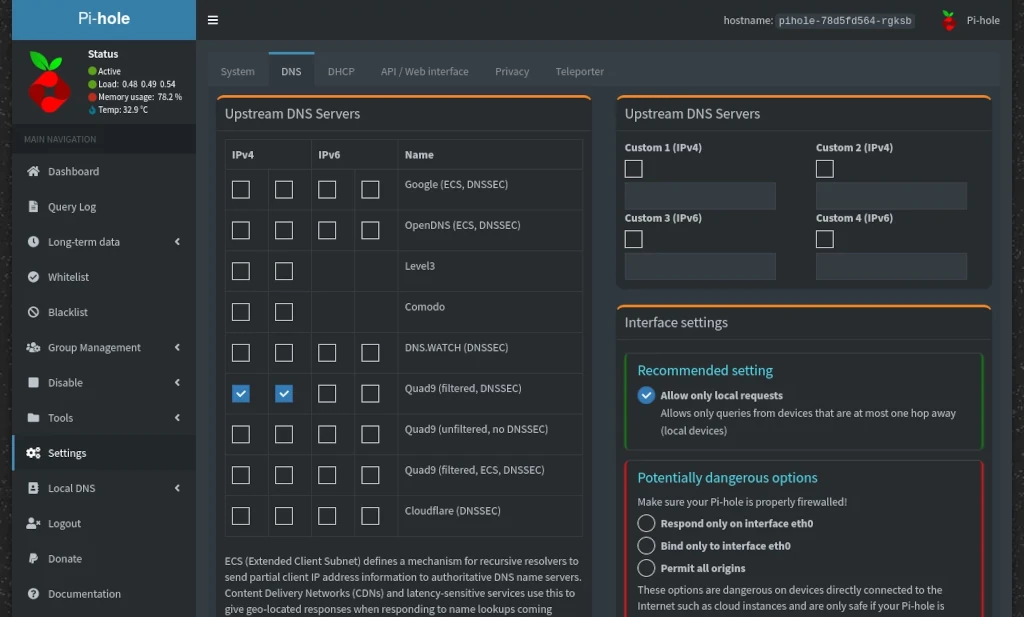
Pi-hole works by functioning as a kind of DNS filter for your home network. DNS stands for Domain Name Service – it’s the thing that translates domain names like techaddressed.com into an IP address so your computer knows how to find the things you want to load from the internet. By default, your Pi-hole doesn’t do this work itself but, instead, you configure it to talk to 3rd party DNS servers (like privacy respecting DNS providers, like Quad9) to get that information.
So if Pi-hole doesn’t do the DNS resolution itself, how exactly does it help protect your privacy? Pi-hole comes bundled with a list of over 100,000 domains that host ads and trackers on the internet. This is where the sinkhole comes into play.
When a device makes a request through the Pi-hole software, Pi-hole checks against the list of domains being requested and prevents resolution to any domains on the block list. Any domains not on the block list have the IP request passed on to the actual DNS servers.
Blocking Advertisements & Trackers
Ad-blocking technology is nothing new – it has existed for many years now and is used by over 25% of Americans online and over 45% of internet users worldwide. Typically, people employ ad-blocking through use of a browser add-on – such as uBlock Origin or Adblock Plus.
So, why use Pi-hole if browser add-ons already exist to do the job? Simple. Pi-hole doesn’t require additional software on your devices and as I’ve previously mentioned, it works for any device on your network.
While installing ad-blocking software on a PC is fairly easy to do, platforms like Android and iOS, for example, don’t make this even remotely easy – by design. It’s in Google and Apple’s interests to allow for as much data collection as legally possible, short of spying on users. If they made it easy for users to deploy ad-blocking tech on their devices it would hurt their and their platform developers bottom lines.
Additionally, internet-of-things and smart devices (such as smart TVs) can often ‘phone home’ to the manufacturer with data about you. A Pi-hole setup can be used to prevent these kinds of data collection as well. See the Forbes article, Shocking: Smart TV Manufacturer Vizio Spies On Customers Using Advanced Big Data Analytics, for an example (spoiler – they also mention LG and Samsung – this isn’t a uniquely Vizio thing).
Besides the default blocking features of Pi-hole, there are additional features you can make use of.
Custom Allow & Block Lists
Sometimes there are domains we want to allow access to that are part of Pi-hole’s block list. For these situations, Pi-hole gives us the ability to create our own custom whitelists (allow) and blacklists (block). Additionally, all lists (including the default ad block list) are able to be assigned to only the specific devices you want.
Examples – I use a custom set of lists to control what websites my son is allowed to visit. I have my desktop PC setup to use the default block list. My wife’s laptop, however … let’s just say she prefers for me to not mess with things.
Again, because Pi-hole is run as an appliance and not as installed software, there’s no limit to which devices you configure controls for.
DHCP Server
Should you choose, It’s possible to use Pi-hole as the DHCP server for your network. The basic features you’d expect are present – being able to specify the IP address range as well as configuring DHCP IP address reservations.
Local DNS
A feature that more advanced users find helpful is the ability to configure your own local DNS entries that are shared to all devices that use the Pi-hole on your network.
Say, for example, you’re a freelance website developer who runs a spare PC as a server on your home network for hosting your work. Using the local DNS in Pi-hole, you can configure a user friendly address to access the sites you’re developing on your network, instead of having to configure a hostname for them inside a host file or even just using the server IP in the URL.
It’s a lot more convenient to type something like http://devwebsite.local/ instead of something like http://192.168.1.100/devwebsite/.
Private DNS Queries
Another feature for more advanced users who are especially privacy conscious and who aren’t afraid to make a few changes to their Pi-hole environment at the operating system level, it’s possible to configure your system to act as a recursive DNS server, making it able to resolve its own DNS queries without the need of a 3rd party DNS provider.
Monitoring
Pi-hole allows you to configure varying degrees of DNS logging – allowing you to see information such as what domains are allowed or blocked the most frequently, or even which devices have accessed what domains. This is especially useful for monitoring what kinds of places your children visit online.
Open Source
Lastly, Pi-hole is open source software – making it both free as-in beer (it costs you nothing) and free as-in speech (you have the rights to the source code – it’s licensed under the European Union Public License ver 1.2).
Is Pi-hole Free?
Absolutely 100% free and open source – released under the European Union Public License (EUPL).
Try It Yourself
If you’ve made it this far, the idea of having better privacy online likely appeals to you. Setting up Pi-hole isn’t terribly difficult. Get yourself a spare computer setup to experiment with and give it a shot. I’ve got a number of posts in this series on different methods to get Pi-hole installed. Decide which works best for you and get started.
If you found this article helpful or have any questions, I encourage you to please share this article with others and/or leave a comment below. If you would like to support our efforts to create additional resources like this, please consider making a donation. Your support is greatly appreciated! Thanks for reading and I hope you visit again soon!